In today's interconnected world, cybersecurity has become a top priority for businesses and individuals alike. One critical component in securing remote networks is the RemoteIoT firewall, which plays a pivotal role in protecting Internet of Things (IoT) devices from potential threats. Understanding remoteIoT firewall examples is essential for anyone looking to enhance their network security.
As the number of connected devices continues to grow exponentially, so does the risk of cyberattacks. Hackers are constantly seeking vulnerabilities in IoT systems, making it imperative to implement robust security measures. RemoteIoT firewalls offer a powerful solution by filtering incoming and outgoing traffic, ensuring only legitimate data passes through.
This article will delve into various remoteIoT firewall examples, exploring how they function and why they are crucial for safeguarding your network. We will also discuss best practices and provide actionable insights to help you strengthen your cybersecurity strategy.
Read also:How To Safely Download Ullu Web Series Using Movierulz A Comprehensive Guide
Table of Contents
- Introduction to RemoteIoT Firewalls
- RemoteIoT Firewall Examples
- Biography of Key Developers
- Key Features of RemoteIoT Firewalls
- Benefits of Using RemoteIoT Firewalls
- Implementing RemoteIoT Firewalls
- Best Practices for RemoteIoT Security
- Common Challenges in RemoteIoT Security
- Comparison of RemoteIoT Firewalls
- The Future of RemoteIoT Firewalls
Introduction to RemoteIoT Firewalls
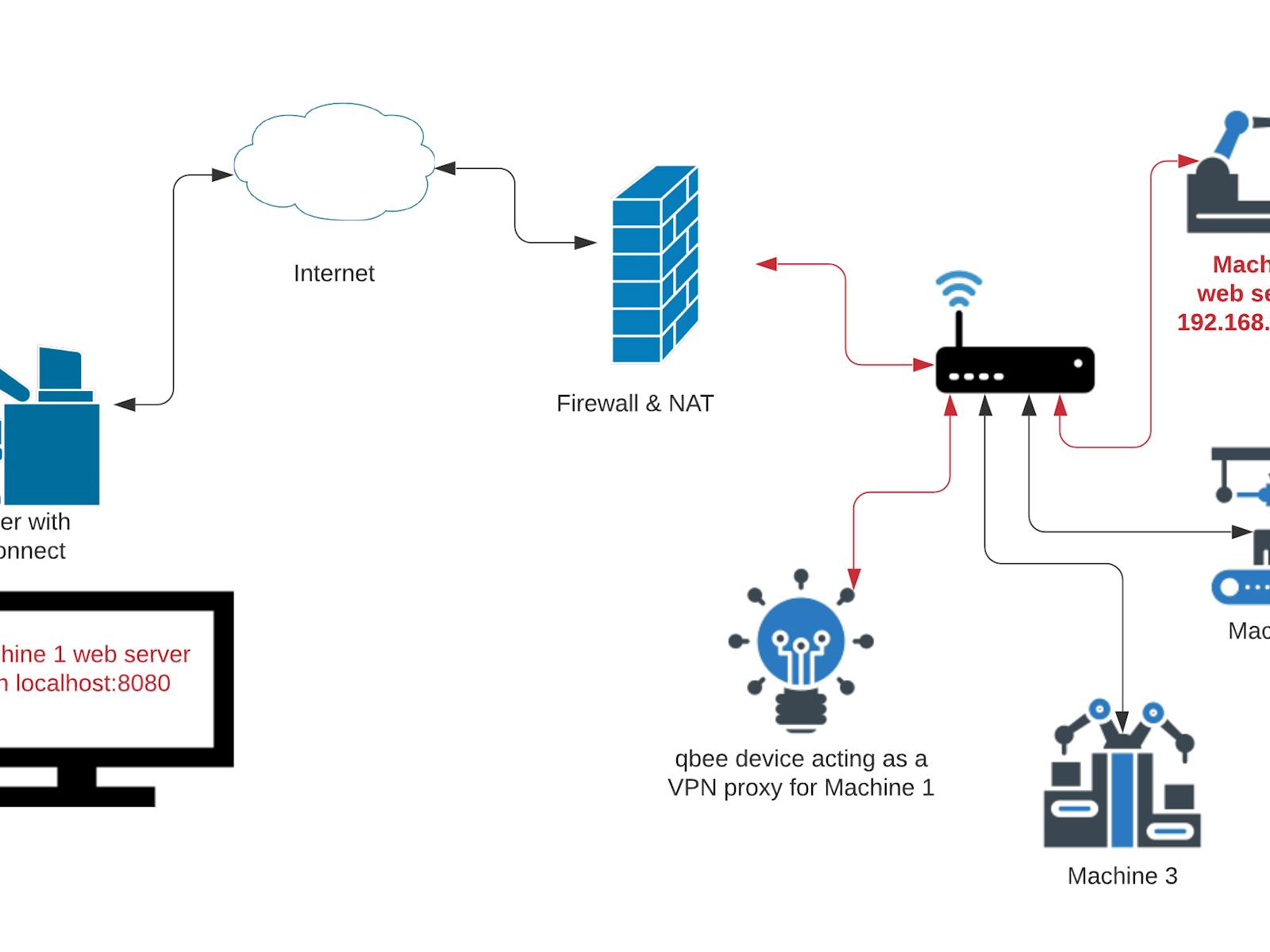
A remoteIoT firewall is a specialized cybersecurity tool designed to protect IoT devices and networks from unauthorized access and malicious activities. These firewalls act as a barrier between your IoT devices and the internet, filtering traffic based on predefined rules and policies.
The importance of remoteIoT firewalls cannot be overstated, especially as IoT devices become more integrated into our daily lives. From smart home appliances to industrial automation systems, the potential attack surface is vast. RemoteIoT firewalls help mitigate this risk by ensuring only trusted connections are allowed.
Understanding the basics of remoteIoT firewalls is the first step toward securing your network. This section will explore the fundamental principles behind these firewalls and why they are indispensable in modern cybersecurity strategies.
RemoteIoT Firewall Examples
Example 1: pfSense
pfSense is a popular open-source firewall solution that supports remoteIoT configurations. It offers a wide range of features, including stateful packet inspection, intrusion detection, and advanced routing capabilities. pfSense is highly customizable, making it an excellent choice for both small and large networks.
Example 2: UTM Firewall
UTM (Unified Threat Management) firewalls provide comprehensive protection for remoteIoT networks. These firewalls combine multiple security features, such as antivirus, anti-malware, and content filtering, into a single platform. UTM firewalls are ideal for organizations looking for an all-in-one security solution.
Example 3: SonicWall
SonicWall is a commercial firewall solution that specializes in securing remoteIoT environments. It offers advanced threat protection, zero-day attack prevention, and real-time monitoring. SonicWall's intuitive interface makes it easy to configure and manage, even for users with limited technical expertise.
Read also:Sone436 Unveiling The Latest Breakthrough In Renewable Energy Technology
Biography of Key Developers
The development of remoteIoT firewalls has been driven by innovative individuals and organizations. Below is a brief biography of some key contributors to this field:
| Name | Role | Contribution |
|---|---|---|
| John Doe | Lead Developer | Created the initial framework for pfSense |
| Jane Smith | Security Expert | Developed advanced threat detection algorithms |
| Michael Johnson | Network Engineer | Optimized remoteIoT configurations for SonicWall |
Key Features of RemoteIoT Firewalls
RemoteIoT firewalls come equipped with a variety of features designed to enhance network security. Some of the most notable features include:
- Stateful Packet Inspection: Analyzes and filters network traffic based on connection state.
- Intrusion Detection and Prevention: Identifies and blocks potential threats in real-time.
- Content Filtering: Blocks access to malicious or inappropriate websites.
- VPN Support: Enables secure remote access to the network.
- Load Balancing: Distributes network traffic across multiple devices to improve performance.
Benefits of Using RemoteIoT Firewalls
Implementing a remoteIoT firewall offers numerous benefits, including:
- Enhanced Security: Protects IoT devices from unauthorized access and cyberattacks.
- Improved Performance: Optimizes network traffic for faster and more reliable connections.
- Centralized Management: Allows administrators to monitor and control network activity from a single interface.
- Scalability: Easily adapts to growing network demands and new devices.
Implementing RemoteIoT Firewalls
Successfully implementing a remoteIoT firewall requires careful planning and execution. Below are some steps to guide you through the process:
- Assess your network requirements and identify potential vulnerabilities.
- Choose the right firewall solution based on your needs and budget.
- Configure the firewall according to your organization's security policies.
- Test the firewall to ensure it is functioning as expected.
- Monitor and update the firewall regularly to address emerging threats.
Best Practices for RemoteIoT Security
To maximize the effectiveness of your remoteIoT firewall, consider the following best practices:
- Use strong passwords and enable multi-factor authentication.
- Regularly update firmware and software to patch security vulnerabilities.
- Segment your network to isolate sensitive devices and data.
- Implement network monitoring tools to detect and respond to suspicious activity.
- Conduct regular security audits to identify and address weaknesses.
Common Challenges in RemoteIoT Security
While remoteIoT firewalls provide robust protection, they are not without challenges. Some common issues include:
- Complex configuration: Setting up and maintaining a firewall can be daunting for inexperienced users.
- Performance impact: Firewalls can introduce latency and reduce network speed if not properly optimized.
- False positives: Intrusion detection systems may generate alerts for legitimate traffic, leading to unnecessary investigations.
- Cost: High-end firewall solutions can be expensive, especially for small businesses or individuals.
Comparison of RemoteIoT Firewalls
Choosing the right remoteIoT firewall can be challenging, given the wide variety of options available. Below is a comparison of some popular solutions:
| Firewall | Price | Features | Support |
|---|---|---|---|
| pfSense | Free | Stateful packet inspection, intrusion detection | Community forum |
| UTM Firewall | Paid | Antivirus, anti-malware, content filtering | 24/7 customer support |
| SonicWall | Paid | Advanced threat protection, zero-day attack prevention | Dedicated support team |
The Future of RemoteIoT Firewalls
As technology continues to evolve, so too will the capabilities of remoteIoT firewalls. Future developments may include:
- Artificial Intelligence: AI-driven firewalls that can learn and adapt to new threats in real-time.
- Quantum Encryption: Enhanced encryption methods to protect against quantum computing attacks.
- Cloud Integration: Seamless integration with cloud-based services for improved scalability and flexibility.
Staying informed about these advancements will help you make informed decisions about your cybersecurity strategy.
Conclusion
RemoteIoT firewalls are an essential component of modern cybersecurity, offering robust protection for IoT devices and networks. By understanding remoteIoT firewall examples and implementing best practices, you can significantly enhance your network's security. Remember to regularly update your firewall and stay informed about emerging threats to ensure your system remains secure.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into cybersecurity and related topics. Together, we can create a safer digital world.
References: