Accessing IoT devices behind a router has become an essential skill for modern-day tech enthusiasts and professionals alike. As more households embrace smart home technology, understanding how to configure and secure IoT devices through routers is paramount. This article will delve into the nuances of accessing IoT devices behind a router, ensuring you can manage and secure your smart devices effectively.
In today's interconnected world, IoT devices are transforming how we interact with technology. From smart thermostats to voice-activated assistants, these devices rely on robust network configurations to function optimally. Accessing IoT devices behind a router is not only about convenience but also about maintaining the security of your network.
This guide will provide you with a detailed understanding of the process, potential challenges, and best practices for accessing IoT devices behind a router. Whether you're a beginner or an advanced user, this article will equip you with the knowledge to enhance your smart home's functionality and security.
Read also:Unveiling The Truth About Movierulzcom Your Comprehensive Guide
Table of Contents
- Introduction to IoT
- Router Configuration
- Port Forwarding
- Using a VPN for IoT Devices
- Security Considerations
- Troubleshooting Tips
- IoT Protocols
- Network Segmentation
- Device Management
- Conclusion
Introduction to IoT
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data. Accessing IoT behind a router is crucial for managing these devices efficiently. Modern routers play a pivotal role in facilitating communication between IoT devices and external networks.
Key benefits of IoT devices include:
- Enhanced automation in homes and businesses
- Improved energy efficiency
- Real-time data monitoring and analysis
However, accessing IoT devices behind a router requires a solid understanding of network configurations and security protocols. This section will lay the groundwork for more advanced topics discussed later in the article.
Router Configuration
Understanding Router Settings
Configuring your router is the first step toward accessing IoT devices behind a router. Modern routers come equipped with user-friendly interfaces that allow you to customize settings to suit your needs. Key router settings include:
- IP address assignment
- Subnet masks
- Default gateway
Ensure that your router's firmware is up to date to take advantage of the latest security features and optimizations. Regular updates also help address vulnerabilities that could compromise your network's security.
Accessing the Router Interface
To access your router's interface, follow these steps:
Read also:Vegamovies20 Your Ultimate Guide To Movie Streaming
- Connect your computer to the router via Ethernet or Wi-Fi.
- Open a web browser and enter the router's IP address (commonly 192.168.1.1 or 192.168.0.1).
- Log in using the default credentials or those you've set previously.
Once logged in, you can configure various settings to optimize your network for IoT devices.
Port Forwarding
Port forwarding is a critical technique for accessing IoT devices behind a router. It allows external devices to communicate with specific devices on your local network by mapping external ports to internal IP addresses. This process is essential for enabling remote access to IoT devices.
Steps to Set Up Port Forwarding:
- Log in to your router's interface.
- Navigate to the port forwarding section.
- Specify the external port, internal IP address, and internal port for the IoT device.
For example, if you're setting up a smart security camera, you might forward port 8080 to the camera's internal IP address. Ensure that the IoT device's IP address is static to maintain consistent communication.
Using a VPN for IoT Devices
What is a VPN?
A Virtual Private Network (VPN) encrypts your internet connection, providing an additional layer of security for IoT devices. By routing IoT traffic through a VPN, you can protect sensitive data from unauthorized access and potential cyber threats.
Benefits of Using a VPN for IoT Devices:
- Data encryption
- Anonymous browsing
- Protection against DDoS attacks
Choosing the Right VPN
When selecting a VPN for IoT devices, consider the following factors:
- Speed and reliability
- Server location
- Encryption protocols
Some popular VPN providers for IoT devices include NordVPN, ExpressVPN, and CyberGhost. Ensure that the VPN you choose supports multiple devices and offers robust security features.
Security Considerations
Securing IoT Devices Behind a Router
Security should be a top priority when accessing IoT devices behind a router. Here are some best practices to enhance your network's security:
- Use strong, unique passwords for all IoT devices and router access.
- Enable two-factor authentication (2FA) wherever possible.
- Regularly update firmware and software for all connected devices.
Additionally, consider implementing a firewall to monitor and control incoming and outgoing network traffic. A well-configured firewall can help prevent unauthorized access to your IoT devices.
Common IoT Security Threats
Understanding potential security threats is crucial for safeguarding your IoT devices. Some common threats include:
- Malware infections
- Botnet attacks
- Data breaches
Stay informed about the latest security trends and vulnerabilities to ensure your network remains secure.
Troubleshooting Tips
Despite careful configuration, issues may arise when accessing IoT devices behind a router. Here are some troubleshooting tips to help resolve common problems:
- Check the router's firmware for updates.
- Verify that port forwarding settings are correct.
- Restart the router and IoT devices.
If the issue persists, consult the device's user manual or contact the manufacturer's support team for further assistance. Documenting your troubleshooting steps can also help identify recurring problems and streamline future resolutions.
IoT Protocols
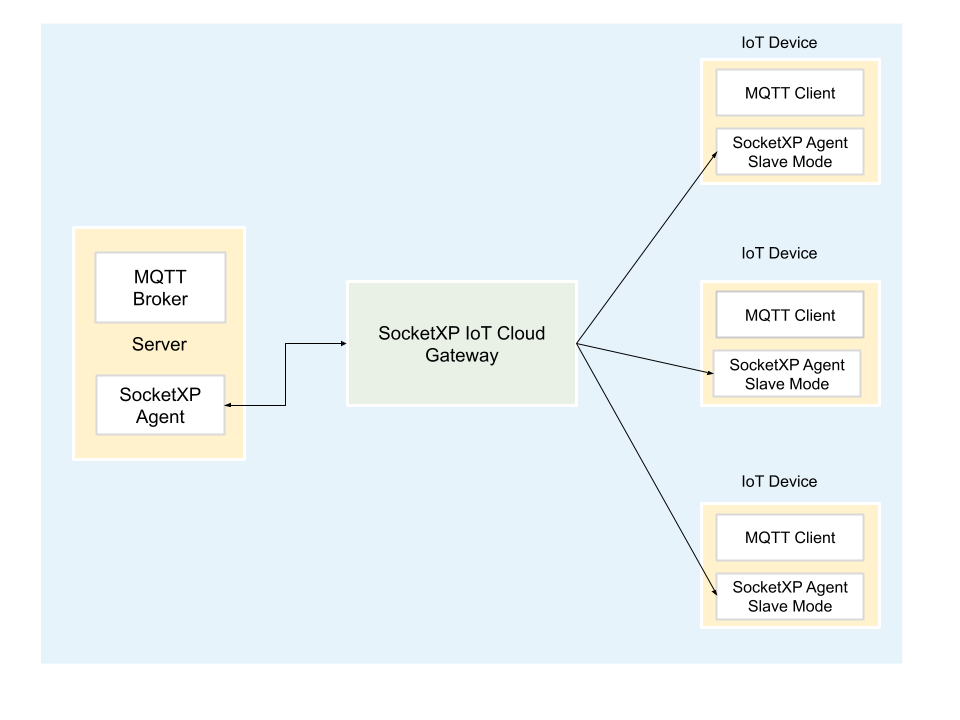
Understanding IoT Communication Protocols
IoT devices communicate using various protocols, each with its own advantages and limitations. Some common IoT protocols include:
- MQTT (Message Queuing Telemetry Transport)
- CoAP (Constrained Application Protocol)
- Zigbee
MQTT is widely used for its lightweight nature and reliability in low-bandwidth environments. CoAP, on the other hand, is ideal for resource-constrained devices. Understanding the protocol your IoT devices use can help optimize network performance and compatibility.
Choosing the Right Protocol
When selecting an IoT protocol, consider factors such as:
- Bandwidth requirements
- Device compatibility
- Security features
Consult the device's documentation to determine the most suitable protocol for your specific use case.
Network Segmentation
Network segmentation involves dividing a network into smaller, isolated segments to enhance security and performance. By segmenting your network, you can limit access to sensitive IoT devices and reduce the attack surface for potential threats.
Benefits of Network Segmentation:
- Improved security
- Enhanced performance
- Streamlined management
Modern routers often include built-in segmentation features, such as guest networks, that allow you to isolate IoT devices from your primary network. Configure these settings carefully to ensure optimal functionality and security.
Device Management
Managing IoT Devices Efficiently
Efficient device management is essential for maintaining a secure and functional IoT network. Use centralized management platforms to monitor and control all connected devices from a single interface. These platforms often provide features such as:
- Device inventory management
- Remote configuration
- Real-time monitoring
Regularly review device logs and performance metrics to identify potential issues and optimize network performance.
Best Practices for Device Management
Adopt the following best practices for effective IoT device management:
- Document all connected devices and their configurations.
- Regularly update device firmware and software.
- Implement strong access controls and authentication mechanisms.
By adhering to these practices, you can ensure your IoT network remains secure and functional over time.
Conclusion
Accessing IoT devices behind a router is a critical skill for anyone managing a smart home or business network. This article has explored various aspects of the process, including router configuration, port forwarding, security considerations, and device management. By following the best practices outlined herein, you can enhance your network's functionality and security.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, consider exploring other articles on our site for more insights into IoT technology and network management. Together, let's build a smarter, more secure digital future!