In today's interconnected world, the best remote IoT firewall examples play a crucial role in securing networks and devices against cyber threats. With the rapid expansion of IoT devices, ensuring robust security measures is more important than ever. This guide dives into the top solutions that can safeguard your IoT ecosystem.
As the Internet of Things (IoT) continues to grow exponentially, so does the risk of cyberattacks. From smart homes to industrial systems, IoT devices are increasingly targeted by malicious actors. Remote IoT firewalls provide an essential layer of protection, filtering out unauthorized access and potential threats.
This article explores the best remote IoT firewall examples available in the market today. We'll analyze their features, benefits, and suitability for different use cases. Whether you're a small business owner or a tech enthusiast, this guide will help you make informed decisions about securing your IoT infrastructure.
Read also:5 Movierulz 2023 Ndash Download Safely And Legally
Table of Contents
- Introduction to Remote IoT Firewalls
- Key Benefits of Remote IoT Firewalls
- Best Remote IoT Firewall Examples
- Deployment Strategies for Remote IoT Firewalls
- Key Considerations When Choosing a Firewall
- Comparing the Best Remote IoT Firewalls
- The Future of Remote IoT Firewalls
- Industry Statistics and Trends
- Enhancing IoT Security Beyond Firewalls
- Conclusion
Introduction to Remote IoT Firewalls
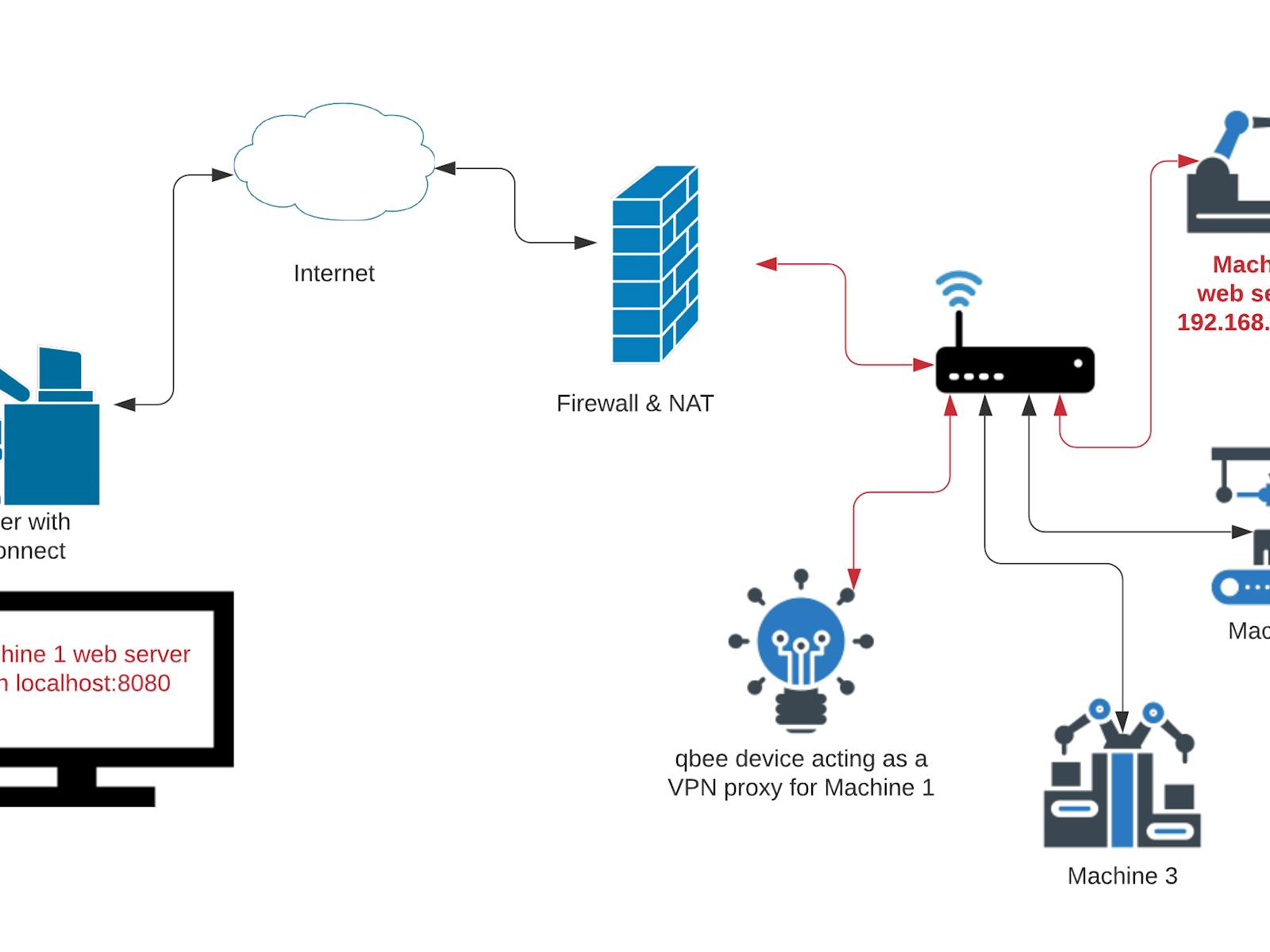
A remote IoT firewall is a specialized cybersecurity solution designed to protect IoT devices and networks from unauthorized access and cyber threats. Unlike traditional firewalls, remote IoT firewalls are tailored to address the unique challenges posed by IoT ecosystems, such as a large number of connected devices, diverse communication protocols, and varying levels of security capabilities.
These firewalls operate by monitoring incoming and outgoing traffic, applying predefined security rules, and blocking malicious activities. They are particularly useful for remote workers, distributed teams, and organizations with geographically dispersed IoT deployments.
With the increasing reliance on IoT devices across industries, remote IoT firewalls have become indispensable tools for maintaining data integrity, privacy, and operational efficiency. This section will explore the fundamental concepts and functionalities of remote IoT firewalls.
Key Benefits of Remote IoT Firewalls
Implementing a remote IoT firewall offers numerous advantages for organizations looking to enhance their cybersecurity posture. Below are some of the key benefits:
- Enhanced Security: Remote IoT firewalls provide an additional layer of protection by filtering out suspicious traffic and blocking unauthorized access.
- Scalability: These solutions are designed to handle large volumes of IoT devices, making them suitable for growing networks.
- Centralized Management: Many remote IoT firewalls offer centralized control, allowing administrators to manage security policies across multiple locations from a single dashboard.
- Compliance: By adhering to industry standards and regulations, remote IoT firewalls help organizations meet compliance requirements.
These benefits make remote IoT firewalls an attractive option for businesses seeking to protect their IoT infrastructure without compromising performance.
Best Remote IoT Firewall Examples
Palo Alto Networks
Palo Alto Networks is a leading provider of next-generation firewalls, including solutions specifically designed for IoT environments. Their remote IoT firewall offerings combine advanced threat prevention, real-time monitoring, and automated policy enforcement.
Read also:Exploring Movierulz Your Ultimate Guide To Movie Downloads And Streaming
Key features of Palo Alto Networks' remote IoT firewalls include:
- Deep packet inspection for comprehensive threat detection.
- Integration with IoT device management platforms for seamless operation.
- Cloud-based management for flexibility and scalability.
With a strong reputation for innovation and reliability, Palo Alto Networks is a top choice for organizations seeking robust IoT security.
Fortinet FortiGate
Fortinet FortiGate is another prominent player in the remote IoT firewall market. Known for its high-performance capabilities, FortiGate offers comprehensive protection for IoT networks, including intrusion prevention, application control, and advanced threat intelligence.
FortiGate's standout features include:
- Unified threat management for simplified security operations.
- Zero-day attack protection through proactive threat detection.
- Support for diverse IoT protocols and devices.
Fortinet's commitment to delivering cutting-edge security solutions makes FortiGate an excellent choice for securing IoT ecosystems.
Check Point IoT Security
Check Point IoT Security is a powerful remote IoT firewall solution that combines cutting-edge technology with user-friendly interfaces. This firewall is designed to protect IoT devices from a wide range of threats, including malware, ransomware, and unauthorized access.
Some of the key features of Check Point IoT Security include:
- Automated device discovery and classification for efficient management.
- Behavioral analysis to detect and mitigate potential threats.
- Integration with existing security frameworks for a cohesive approach.
Check Point's focus on innovation and customer satisfaction has earned it a prominent position in the IoT security landscape.
Sophos XG Firewall
Sophos XG Firewall is a versatile remote IoT firewall solution that offers comprehensive protection for IoT networks. With its advanced threat detection capabilities and intuitive management tools, Sophos XG Firewall is ideal for organizations of all sizes.
Key features of Sophos XG Firewall include:
- Artificial intelligence-driven threat analysis for proactive defense.
- Wireless network security for IoT devices connected via Wi-Fi.
- Comprehensive reporting and analytics for informed decision-making.
Sophos' dedication to delivering reliable and effective security solutions has made XG Firewall a popular choice among IoT professionals.
Deployment Strategies for Remote IoT Firewalls
Successfully deploying a remote IoT firewall requires careful planning and execution. Below are some best practices for implementing these solutions:
- Assess Your Network Needs: Begin by evaluating your IoT infrastructure to identify potential vulnerabilities and security requirements.
- Select the Right Solution: Choose a remote IoT firewall that aligns with your organization's size, budget, and security goals.
- Implement a Phased Rollout: Gradually deploy the firewall across your network to minimize disruption and ensure smooth integration.
- Monitor and Optimize: Continuously monitor firewall performance and adjust settings as needed to maintain optimal security.
By following these strategies, organizations can maximize the effectiveness of their remote IoT firewalls and protect their IoT ecosystems from evolving threats.
Key Considerations When Choosing a Firewall
When selecting a remote IoT firewall, there are several factors to consider:
- Compatibility: Ensure the firewall is compatible with your existing IoT devices and infrastructure.
- Scalability: Choose a solution that can grow with your organization's needs.
- Support: Opt for a vendor that offers reliable customer support and regular updates.
- Cost: Evaluate the total cost of ownership, including initial purchase, maintenance, and potential upgrades.
By carefully weighing these considerations, organizations can select a remote IoT firewall that meets their unique requirements and budget constraints.
Comparing the Best Remote IoT Firewalls
To help you make an informed decision, here's a comparison of the top remote IoT firewalls:
| Firewall | Key Features | Best For |
|---|---|---|
| Palo Alto Networks | Deep packet inspection, cloud-based management | Large enterprises with complex IoT networks |
| Fortinet FortiGate | Unified threat management, zero-day attack protection | Organizations requiring high-performance security |
| Check Point IoT Security | Automated device classification, behavioral analysis | Businesses prioritizing ease of use and automation |
| Sophos XG Firewall | AI-driven threat detection, wireless network security | Smaller organizations seeking cost-effective solutions |
This comparison highlights the strengths and ideal use cases for each solution, enabling you to choose the best option for your needs.
The Future of Remote IoT Firewalls
As IoT technology continues to evolve, so too will the capabilities of remote IoT firewalls. Emerging trends such as artificial intelligence, machine learning, and edge computing are expected to play a significant role in shaping the future of IoT security.
Upcoming advancements in remote IoT firewalls may include:
- Enhanced threat intelligence through AI and machine learning.
- Improved integration with edge devices for faster response times.
- Increased automation to reduce manual intervention and improve efficiency.
By staying informed about these developments, organizations can prepare for the next generation of IoT security solutions.
Industry Statistics and Trends
According to recent studies, the global IoT security market is expected to grow significantly in the coming years. Below are some key statistics and trends:
- By 2025, the number of IoT devices is projected to exceed 75 billion globally.
- The IoT security market is anticipated to reach $30 billion by 2027, driven by increasing cyber threats and regulatory requirements.
- Remote IoT firewalls are becoming increasingly popular, with adoption rates rising across various industries, including healthcare, manufacturing, and transportation.
These statistics underscore the growing importance of remote IoT firewalls in securing the expanding IoT landscape.
Enhancing IoT Security Beyond Firewalls
While remote IoT firewalls are essential for protecting IoT networks, they should be part of a broader security strategy. Additional measures to enhance IoT security include:
- Implementing strong authentication and encryption protocols.
- Regularly updating firmware and software to address known vulnerabilities.
- Conducting routine security audits and penetration testing.
By adopting a holistic approach to IoT security, organizations can better protect their devices and data from emerging threats.
Conclusion
In conclusion, the best remote IoT firewall examples offer robust protection for IoT networks and devices. Solutions like Palo Alto Networks, Fortinet FortiGate, Check Point IoT Security, and Sophos XG Firewall provide essential features and functionalities to address the unique challenges of IoT security.
To ensure the safety of your IoT ecosystem, consider implementing a remote IoT firewall that aligns with your organization's needs and budget. Additionally, adopt a comprehensive security strategy that includes regular updates, audits, and employee training.
We encourage you to share your thoughts and experiences with remote IoT firewalls in the comments section below. For more insights into IoT security, explore our other articles and resources. Stay safe and secure in the ever-evolving world of IoT!